GopherWhisper APT Campaign Emerges with Advanced Go-Based Arsenal
Security researchers have identified a sophisticated China-linked advanced persistent threat group dubbed GopherWhisper that's actively targeting government networks using an arsenal of Go-based malware tools. The threat actor has been observed deploying multiple custom backdoors alongside specialized loaders and injectors designed to maintain persistent access to compromised systems while evading detection mechanisms.
The campaign represents a significant evolution in APT tactics, with GopherWhisper demonstrating advanced operational security by leveraging legitimate cloud services and platforms for command and control communications. This approach allows the attackers to blend malicious traffic with normal business communications, making detection considerably more challenging for traditional security monitoring systems.
The group's malware toolkit centers around Go-based backdoors that provide comprehensive remote access capabilities to compromised systems. These tools are complemented by custom loaders that facilitate initial deployment and injectors that enable the malware to establish persistence within target environments. The use of the Go programming language offers several advantages for attackers, including cross-platform compatibility and the ability to compile to standalone executables that don't require runtime dependencies.
Intelligence analysts have traced the campaign's infrastructure and tactics to known China-linked threat actors, though the specific attribution remains under investigation. The targeting pattern focuses heavily on government entities, suggesting intelligence collection as the primary motivation behind these intrusions. The sophisticated nature of the tools and the operational discipline demonstrated by the attackers indicate this is likely a state-sponsored or state-affiliated group with significant resources and technical capabilities.
Government Entities Face Targeted Espionage Campaign
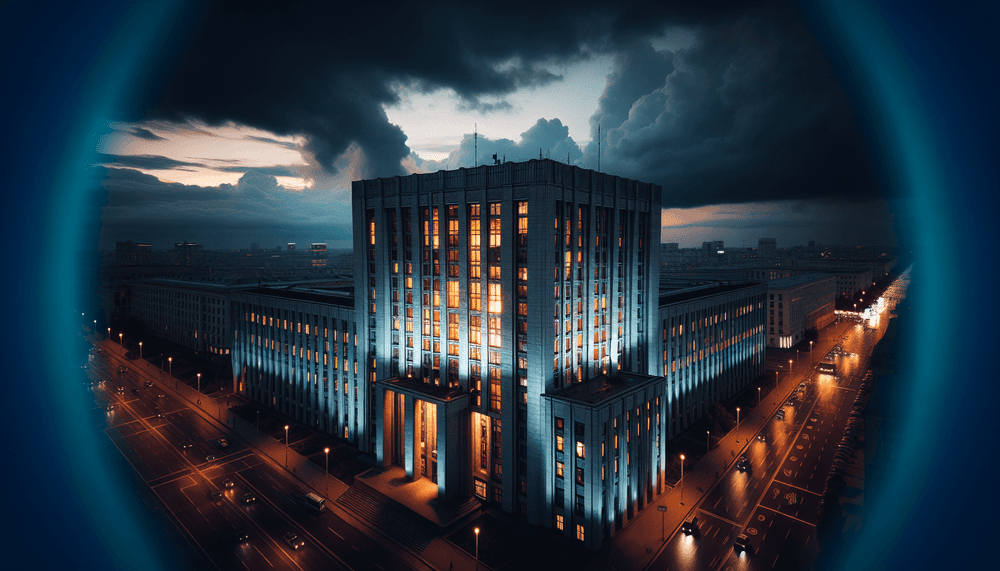
The GopherWhisper campaign primarily targets government organizations across multiple sectors, with particular focus on agencies handling sensitive national security information and policy development. The threat actor has demonstrated the capability to compromise both federal and regional government networks, suggesting a broad intelligence collection mandate that spans various levels of government administration.
The attack methodology indicates that organizations with limited cybersecurity resources are particularly vulnerable to this campaign. Government entities that rely heavily on cloud-based services and remote access solutions face elevated risk, as the attackers specifically abuse legitimate platforms to establish their command and control infrastructure. This targeting approach makes the malicious activity significantly harder to distinguish from normal business operations.
Security teams at government organizations should be particularly concerned about the persistent nature of these attacks. The custom loaders and injectors used by GopherWhisper are designed to maintain long-term access to compromised systems, potentially allowing attackers to monitor communications, exfiltrate sensitive documents, and track policy developments over extended periods. The Go-based backdoors provide comprehensive system access, enabling attackers to move laterally through networks and escalate privileges as needed to achieve their intelligence objectives.
Defending Against GopherWhisper's Advanced Persistence Techniques
Government organizations must implement comprehensive detection and response strategies to counter the GopherWhisper threat. The group's reliance on legitimate services for command and control requires security teams to implement advanced behavioral analysis and anomaly detection capabilities that can identify suspicious patterns in otherwise normal network traffic. Organizations should deploy endpoint detection and response solutions capable of identifying Go-based malware and monitoring for the specific indicators of compromise associated with this campaign.
Network segmentation becomes critical when defending against persistent threats like GopherWhisper. Government entities should implement zero-trust network architectures that limit lateral movement opportunities and require continuous authentication for access to sensitive systems. Regular security assessments and penetration testing can help identify potential entry points that attackers might exploit to deploy their custom loaders and establish initial footholds within target networks.
The CISA Known Exploited Vulnerabilities catalog provides essential guidance for government organizations seeking to reduce their attack surface against sophisticated threat actors. Security teams should prioritize patching systems and implementing the security controls outlined in CISA advisories to prevent initial compromise. Additionally, organizations should monitor for the specific file signatures and network patterns associated with Go-based malware, as these tools often exhibit distinctive characteristics that can aid in detection and response efforts.