Why Deploy KB5079391 Through WSUS Instead of Direct Installation?
Microsoft's KB5079391 represents a significant cumulative update for Windows 11 24H2 and 25H2 systems, bringing 29 improvements including Smart App Control enhancements and display optimizations. While individual systems can download this update directly from Windows Update, enterprise environments require controlled, phased deployment strategies to minimize business disruption and ensure system stability across hundreds or thousands of endpoints.
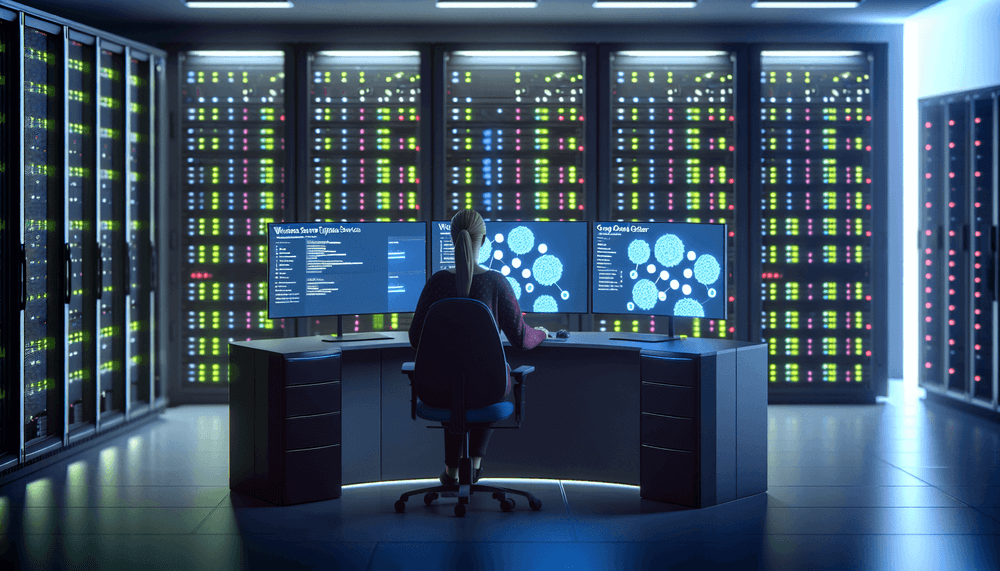
WSUS (Windows Server Update Services) combined with Group Policy provides the enterprise-grade control needed for large-scale update deployment. This approach allows you to test updates on pilot systems, create deployment rings for gradual rollout, and maintain centralized visibility into installation progress. Most importantly, it gives you the ability to halt deployment immediately if issues arise and implement automated rollback procedures across your entire fleet.