Chinese APT Group Infiltrates Critical Telecom Backbone Systems
Security researchers discovered a sophisticated Chinese state-sponsored threat actor operating deep within telecom backbone infrastructure on March 26, 2026. The attackers deployed advanced kernel-level implants and passive backdoors designed for long-term persistence and high-level espionage operations. The campaign represents one of the most significant compromises of critical communications infrastructure discovered this year.
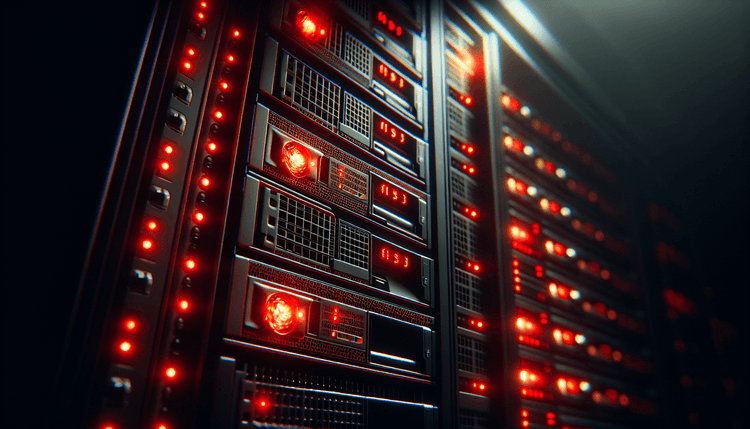
The threat group gained access to core telecom systems that handle routing and switching for major communications networks. These backbone systems process massive volumes of voice, data, and internet traffic, making them prime targets for nation-state actors seeking intelligence collection capabilities. The attackers demonstrated advanced technical capabilities by successfully deploying kernel-mode rootkits that operate at the deepest levels of the operating system.
Kernel implants represent the most sophisticated form of malware persistence, as they run with the highest system privileges and can intercept virtually any activity on the compromised systems. These implants are extremely difficult to detect using traditional security tools because they operate below the level of most monitoring software. The passive backdoors discovered alongside the kernel implants suggest the attackers prioritized stealth and long-term access over immediate data exfiltration.
The discovery highlights the ongoing threat that state-sponsored groups pose to critical infrastructure. Telecom backbone systems are particularly attractive targets because they provide access to communications metadata, routing information, and potentially the ability to intercept or manipulate network traffic. The CISA Known Exploited Vulnerabilities catalog has documented numerous instances of nation-state actors targeting telecom infrastructure over the past several years.
Related: Teams Phishing Campaign Deploys A0Backdoor Malware
Related: Chinese APT Targets Asian Military Networks in Multi-Month
Related: Chinese APT Targets Asian Organizations in Multi-Year
Security researchers who uncovered the intrusion noted that the attackers had likely maintained access for an extended period before detection. The sophisticated nature of the kernel implants and the careful deployment of passive backdoors suggests this was a well-resourced operation with strategic intelligence objectives rather than a financially motivated attack.
Telecom Backbone Infrastructure Under State-Sponsored Surveillance
The compromise affects critical telecom backbone infrastructure that forms the foundation of modern communications networks. These systems handle routing decisions for internet traffic, voice communications, and data transmission across regional and national networks. The affected infrastructure likely processes communications for millions of users, though the full scope of the compromise remains under investigation.
Telecom backbone systems typically run on specialized hardware and software platforms designed for high-availability operations. These systems often use custom operating systems or hardened versions of commercial platforms, making the successful deployment of kernel implants particularly concerning. The attackers would have needed detailed knowledge of the target systems' architecture and likely exploited zero-day vulnerabilities or supply chain compromises to achieve kernel-level access.
The passive nature of the backdoors suggests the attackers were primarily focused on intelligence collection rather than service disruption. This approach allows them to monitor communications patterns, collect metadata about network traffic, and potentially identify high-value targets for further surveillance. The strategic value of this access to a nation-state actor cannot be overstated, as it provides insights into communications infrastructure that could be leveraged for both intelligence gathering and potential future cyber operations.
Organizations operating telecom infrastructure should immediately review their security monitoring capabilities and conduct thorough assessments of their core network systems. The discovery of this compromise demonstrates that even the most critical infrastructure systems remain vulnerable to determined state-sponsored attackers with advanced capabilities.
Advanced Kernel Implants Enable Persistent Telecom Espionage
The Chinese threat actors employed sophisticated kernel-level implants that operate with the highest system privileges, allowing them to intercept system calls, network traffic, and potentially modify system behavior without detection. Kernel implants are particularly dangerous because they run in kernel space, where they have unrestricted access to system resources and can hide their presence from user-mode security tools.
The passive backdoors discovered alongside the kernel implants were designed to maintain long-term access while minimizing the risk of detection. Unlike active backdoors that regularly communicate with command and control servers, passive backdoors wait for specific triggers or conditions before activating. This approach significantly reduces network signatures that security monitoring tools might detect.
Organizations should immediately implement enhanced monitoring for kernel-level activities and unusual system behavior. This includes deploying endpoint detection and response tools capable of kernel-level visibility, implementing hypervisor-based security solutions, and establishing baseline monitoring for critical system processes. The Microsoft Security Response Center provides guidance on implementing kernel protection mechanisms for Windows-based systems.
Detection strategies should focus on identifying anomalous kernel module loads, unexpected system call patterns, and unusual network behavior from critical infrastructure systems. Organizations should also implement code signing verification for all kernel modules and drivers, as the attackers likely used signed malicious drivers or exploited vulnerabilities in legitimate signed drivers to achieve kernel access.
Incident response teams should conduct thorough forensic analysis of potentially affected systems, including memory dumps and kernel-level artifacts. The sophisticated nature of these implants means that traditional file-based scanning may not detect their presence, requiring specialized forensic techniques and tools designed for kernel-level malware analysis.