Cisco Releases Emergency Patches for Critical IMC Security Flaws
Cisco disclosed and patched several critical security vulnerabilities on April 2, 2026, including a severe authentication bypass flaw affecting the company's Integrated Management Controller (IMC) systems. The most serious vulnerability allows remote attackers to completely circumvent authentication mechanisms and gain full administrative privileges on affected IMC instances without requiring any user credentials or prior system access.
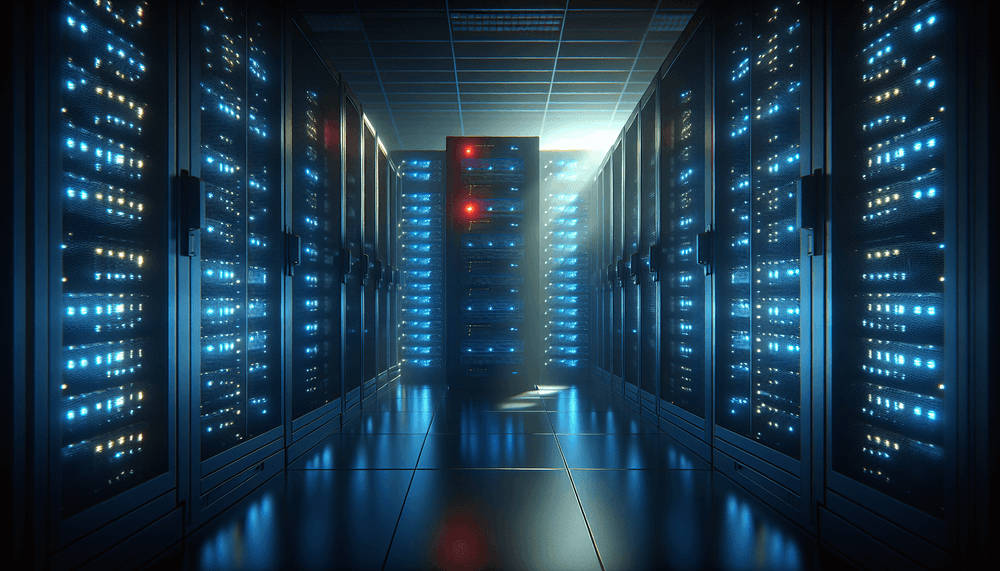
The Integrated Management Controller serves as a critical component in Cisco's server infrastructure, providing out-of-band management capabilities for UCS servers and other enterprise hardware. This controller operates independently of the main server operating system, making it a high-value target for attackers seeking persistent access to corporate infrastructure. The authentication bypass vulnerability essentially renders all configured security controls useless, as attackers can assume complete control over the management interface.
Cisco's Product Security Incident Response Team (PSIRT) coordinated the disclosure following responsible vulnerability reporting protocols. The company has confirmed that these vulnerabilities were discovered through internal security assessments and external security research, though specific details about the discovery timeline remain limited. The patches were developed and tested over several weeks before today's coordinated release, indicating the severity of the underlying security flaws.
The vulnerability affects the web-based management interface of IMC systems, which administrators typically use to configure server settings, monitor hardware health, and perform remote management tasks. Successful exploitation would allow attackers to modify BIOS settings, access sensitive configuration data, deploy malicious firmware, or use the compromised IMC as a pivot point for lateral movement within enterprise networks. The attack vector appears to be network-based, meaning any IMC system accessible over corporate networks or the internet could potentially be compromised.
Related: Cisco Patches Critical IOS Vulnerabilities in March 2026
Related: HPE AOS-CX Flaw Lets Attackers Reset Admin Passwords
Related: HPE Patches Five Critical AOS-CX Flaws: RCE, Privilege
Related: TP-Link Patches Critical Router Flaws Enabling RCE
Related: Oracle Patches Critical RCE Flaw in Identity Manager
Enterprise Organizations Running Cisco UCS Infrastructure at Risk
The authentication bypass vulnerability primarily affects organizations running Cisco Unified Computing System (UCS) servers with vulnerable IMC firmware versions. Enterprise data centers, cloud service providers, and managed hosting facilities represent the highest-risk environments, as these organizations typically deploy large numbers of UCS servers with IMC controllers exposed to internal management networks. Organizations that have enabled remote management capabilities or exposed IMC interfaces to external networks face elevated risk of exploitation.
Cisco has not yet published a complete list of affected IMC firmware versions, but preliminary analysis suggests that multiple generations of UCS hardware could be vulnerable. This includes UCS B-Series blade servers, C-Series rack servers, and potentially newer X-Series systems depending on their IMC implementation. Organizations should assume all IMC-enabled systems are potentially affected until Cisco releases detailed version information and vulnerability matrices.
The scope of potential impact extends beyond individual server compromise. IMC controllers often have privileged access to server hardware, BIOS configurations, and network interfaces. Successful attacks could enable persistent malware installation, credential harvesting from server memory, or complete system takeover that survives operating system reinstallation. For organizations operating critical infrastructure or handling sensitive data, compromised IMC systems represent a significant security breach that could facilitate long-term advanced persistent threat (APT) activities.
Immediate Patching Required for All Cisco IMC Systems
Cisco strongly recommends immediate application of the security patches released today across all IMC-enabled systems. Organizations should prioritize patching based on network exposure, with internet-facing or DMZ-connected IMC systems requiring urgent attention. The patching process typically involves downloading updated firmware from Cisco's support portal and applying it through the IMC web interface or command-line tools, though specific procedures vary by hardware model and current firmware version.
Until patches can be applied, organizations should implement network-level mitigations to reduce attack surface. This includes restricting IMC network access through firewall rules, disabling unnecessary IMC services, and implementing additional authentication layers where possible. Network segmentation should isolate IMC management traffic from general corporate networks, and monitoring systems should be configured to detect unusual IMC access patterns or configuration changes.
Cisco has indicated that additional security advisories may follow as the company completes its comprehensive security review of IMC systems. Organizations should monitor the CISA Known Exploited Vulnerabilities catalog for any updates regarding active exploitation of these vulnerabilities. System administrators should also review IMC access logs for suspicious activity and consider rotating administrative credentials as a precautionary measure following patch deployment.