Formula 1 Teams Transform Security Operations for Racing Speed
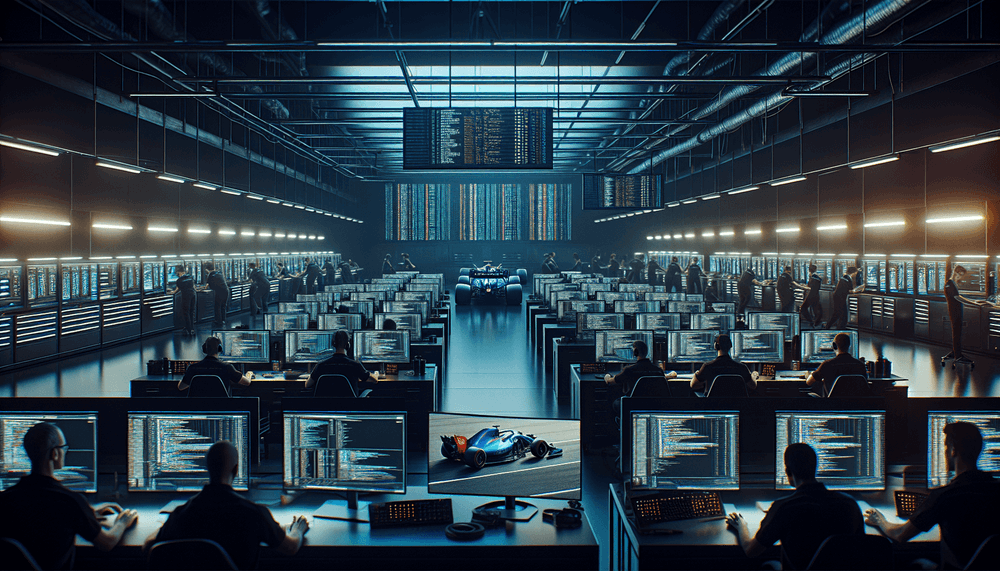
Formula 1 racing teams have implemented comprehensive DevSecOps automation frameworks to deliver security updates and patches at the same velocity required for competitive motorsport engineering. The initiative, launched across multiple F1 teams in April 2026, represents a fundamental shift from traditional security review processes to real-time automated security integration that matches the millisecond precision demands of professional racing.
The transformation addresses the unique challenge facing F1 teams where engineering staff must deploy critical software updates, telemetry patches, and security fixes within extremely compressed timeframes during race weekends. Traditional security review cycles that might take days or weeks in corporate environments simply cannot accommodate the rapid iteration cycles required when teams need to push aerodynamic simulation updates, engine management patches, or data acquisition fixes between practice sessions.
F1 teams have historically operated with custom-built engineering systems that process massive volumes of telemetry data from sensors measuring everything from tire pressure to aerodynamic flow patterns. These systems require constant updates as teams develop new performance optimizations, but the critical nature of race-day operations means any security vulnerability could potentially compromise competitive advantage or safety systems. The new DevSecOps approach embeds security scanning, vulnerability assessment, and compliance checking directly into the continuous integration pipelines that F1 engineers use to deploy updates to car systems and trackside infrastructure.
The implementation leverages containerized deployment strategies where security policies are enforced at the infrastructure level, allowing engineering teams to maintain their rapid development pace while ensuring that all code changes undergo automated security validation. This approach has enabled teams to reduce security review cycles from hours to minutes, matching the operational tempo required during race weekends when teams might need to deploy critical fixes between qualifying sessions.
F1 Engineering Teams and Motorsport Technology Ecosystem
The DevSecOps transformation directly impacts IT and engineering departments across all Formula 1 teams, affecting approximately 2,000 technical staff members who work on car development, race strategy systems, and trackside operations. Each F1 team employs between 60-100 engineers who regularly deploy software updates to systems ranging from engine control units to aerodynamic simulation platforms, all of which now benefit from automated security integration.
The change particularly affects race engineers who manage real-time telemetry systems during Grand Prix weekends, where they must process and respond to thousands of data points per second while ensuring system integrity. Previously, any security-related code changes required manual review processes that could delay critical updates needed for optimal car performance. The automated security pipeline now allows these engineers to maintain their focus on performance optimization while security validation occurs transparently in the background.
Beyond the immediate F1 ecosystem, the implementation serves as a model for other high-performance industries where rapid deployment cycles are essential. Aerospace companies, defense contractors, and financial trading firms face similar challenges where security requirements must be balanced against operational velocity demands. The motorsport industry's adoption of DevSecOps automation demonstrates how security can be integrated without compromising the speed requirements of mission-critical operations.
Implementation Strategy and Technical Architecture
F1 teams have deployed comprehensive security automation frameworks built around containerized microservices architectures that enable rapid deployment while maintaining security controls. The implementation utilizes automated vulnerability scanning tools integrated directly into GitLab CI/CD pipelines, where every code commit triggers security analysis including static application security testing (SAST), dynamic application security testing (DAST), and dependency vulnerability scanning through tools like Snyk and Veracode.
The technical architecture incorporates infrastructure-as-code principles where security policies are defined as code and automatically enforced across all deployment environments. Teams utilize Kubernetes clusters with Pod Security Standards and network policies that automatically isolate workloads and enforce least-privilege access controls. This approach allows engineering teams to deploy updates to critical systems like telemetry processors and strategy optimization algorithms while ensuring that security boundaries remain intact even during rapid iteration cycles.
Race teams have implemented automated compliance checking that validates all deployments against FIA technical regulations and internal security standards before code reaches production systems. The framework includes automated rollback capabilities that can instantly revert problematic deployments if security violations are detected, ensuring that competitive operations continue uninterrupted. Teams also utilize CISA's Known Exploited Vulnerabilities catalog for automated vulnerability intelligence that helps prioritize security updates based on active threat landscapes.
The implementation includes comprehensive logging and monitoring through security information and event management (SIEM) systems that track all deployment activities and security events in real-time. This visibility enables teams to maintain audit trails required for regulatory compliance while providing security teams with the data needed to continuously improve automated security controls. The approach has enabled F1 teams to achieve security deployment cycles that match their engineering velocity requirements while maintaining the rigorous security standards necessary for protecting competitive intellectual property and ensuring operational safety.