Cybersecurity News, Threats & Vulnerability Alerts

Medusa Ransomware Exploits Zero-Days Within Days
Medusa ransomware operators weaponize fresh vulnerabilities and encrypt victim networks within days of initial compromise.
German Police ID Russian Leaders of REvil Ransomware Gang
German Federal Police identified two Russian nationals as leaders of GandCrab and REvil ransomware operations that caused billions in damages worldwide.
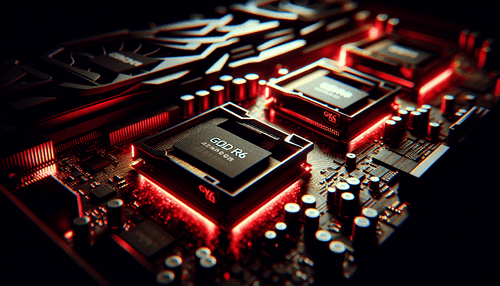
GPUBreach Attack Exploits GDDR6 Memory for System Takeover
Researchers demonstrate GPUBreach attack that triggers Rowhammer bit-flips in GPU GDDR6 memory to escalate privileges and compromise systems.
Iran-Linked Hackers Target Microsoft 365 in Israel and UAE
Iran-nexus threat actors launched password-spraying attacks against Microsoft 365 environments in Israel and UAE during March 2026.
Storm-1175 Deploys Zero-Day Exploits in Medusa Ransomware Attacks
Microsoft warns that China-based Storm-1175 cybercriminal group is deploying zero-day and n-day exploits in high-velocity Medusa ransomware campaigns targeting organizations worldwide.
UAT-10608 Hackers Target Next.js Apps with React2Shell Tool
Threat group UAT-10608 exploits vulnerable Next.js applications using React2Shell automation to steal credentials and system secrets.

Fake Court Traffic Violation Texts Target US Drivers
Scammers impersonate state courts nationwide with fake traffic violation texts containing malicious QR codes to steal payment data.
Fortinet Patches Critical FortiClient EMS Zero-Day Under Attack
Fortinet released emergency patches for CVE-2026-35616, a critical FortiClient EMS vulnerability actively exploited by attackers worldwide.

CVE-2025-55182 Exploited in Mass Credential Theft Campaign
Attackers exploit React2Shell vulnerability in Next.js applications to steal credentials through automated large-scale campaign targeting web developers.

Axios HTTP Client Targeted by North Korean Social Engineering
Axios HTTP client maintainers reveal detailed post-mortem of sophisticated North Korean social engineering attack targeting their development team.

Hims & Hers Health Discloses Data Breach via Third-Party Platform
Telehealth company Hims & Hers Health suffered a data breach when attackers stole customer support tickets from a third-party service platform.
Progress ShareFile RCE Flaws Enable Pre-Auth Server Takeover
Critical Progress ShareFile vulnerabilities allow attackers to chain exploits for unauthenticated remote code execution and arbitrary file uploads.
EU Attributes Commission Cloud Hack to TeamPCP Group
CERT-EU confirms TeamPCP threat group breached European Commission cloud infrastructure, exposing data from 29 Union entities.
Vidar Malware Exploits Claude Code Leak via Fake GitHub Repos
Threat actors leverage Anthropic's Claude Code source leak to distribute Vidar information-stealing malware through malicious GitHub repositories targeting developers.
React2Shell Flaw Exploited in Mass Credential Theft Campaign
Cisco Talos discovered attackers exploiting React2Shell vulnerability to steal AWS secrets, SSH keys, and GitHub tokens at scale.
North Korean Hackers Drain $285M from Drift Protocol
North Korean threat actors executed a sophisticated attack draining $285 million from Drift Protocol's treasury in under 10 seconds.

Casbaneiro Banking Trojan Targets Spanish-Speaking Users
Casbaneiro banking Trojan launches sophisticated campaigns targeting Spanish speakers with advanced evasion techniques and rapid replication capabilities.
Cisco Patches Critical IMC Authentication Bypass Flaw
Cisco fixed multiple critical vulnerabilities including an authentication bypass in Integrated Management Controller granting admin access.

WhatsApp Alerts 200 Users Hit by Fake iOS App Spyware
WhatsApp warned approximately 200 users who installed a malicious fake iOS app containing government-grade spyware targeting Italian citizens.
CrystalRAT Malware-as-a-Service Emerges on Telegram
New CrystalRAT malware-as-a-service platform launches on Telegram with remote access, data theft, and keylogging capabilities targeting Windows systems.
TrueConf Zero-Day Exploited to Execute Files on Endpoints
Attackers exploit a zero-day vulnerability in TrueConf conference servers to execute arbitrary files on all connected endpoints.

